I was testing a couple of conditional access policies against specific Office 365 cloud applications and came across a weird situation when doing a what-if analysis. Let’s take a simple scenario of blocking access to Exchange Online if the user is is not in our trusted IP list. Doing a what-if analysis, it works as expected when I test my account against that application.

Now, let’s setup a CAP targeting Teams and do a what-if analysis.

Both Exchange and Teams CAP will be applied, even though I am only targeting Teams. After digging more into this, there are service dependencies for conditional access based on the application being used. Looking at Teams, the user needs to satisfy access to SharePoint and Exchange before signing into Teams.
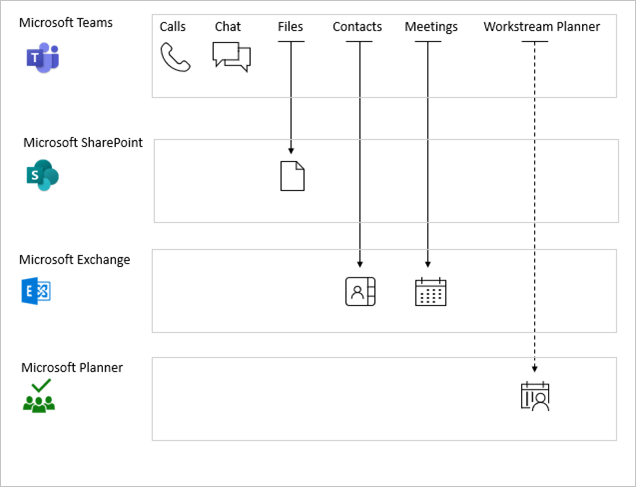
Trying to figure out why this happens lead me to https://learn.microsoft.com/en-us/azure/active-directory/conditional-access/service-dependencies which has the screenshot you saw above. They have this nifty tip 🙂
Most organizations will target the Office 365 app and not individual applications in their CAPs. Just keep this little tidbit in the back of your head not to get blindsided when doing CAP work. 🙂


